-
The Intuitive Index
The Challenges in Creating a User Friendly Website One of the common objectives that we hear from associations who are planning a website redesign is that you want the website to be more user friendly and "intuitive." What makes a website intuitive is multi-fauceted though, it's not just one thing. For example: What's intuitive for a person with sight may not be intuitive for a blind user. What makes your website intuitive for a member who uses it on an almost daily basis may not be intuitive...
-
What is Custom WordPress development and why you want it
Do you have a WordPress website you generate income with? Then you certainly want to stand out in front of people looking for your services. This starts with moving away from basic WordPress and maximizing your potential with Custom WordPress Development. What is custom WordPress development? Custom WordPress development is the development, design and implementation of unique features aligned with a business's unique needs, strategies and goals. Compared to just another WordPress site on the web,...
-
Is WordPress secure: Dos & Don'ts
For many people contemplating hosting their websites through WordPress, The big question stands. "Is WordPress secure?" Even though Wordfence's 2021 report attested that there are approximately 2 800 attacks on websites per second, for the most part, WordPress is secure. It just happens to be an open source software. This means the code WordPress is built on is available to you as well as hackers. This is probably why WordPress is the number one targeted CMS by hackers. Even so, each...
-
WordPress designer vs Developer: When to hire either?
Two people you are guaranteed to need as a WordPress site owner; a WordPress designer and a WordPress developer. When you might need either depends on the plans you have for your website and your goals. But when it comes down to it, you have to be clear on your site’s goals to figure out who exactly has the skills to implement the goals between a WordPress designer and developer. In this article we are going to talk about the difference between a WordPress designer and a WordPress developer. By...
-
Reasons to hire a WordPress developer as an employee
Many small businesses start off with the same thing in common: they have limited needed skills to grow the business. The owner has to wear all the hats and be a marketer, writer, project manager, operations, etc while also keeping the business afloat. On top of that, there's the hassle of the website you operate your business through. A vital part of your business’s success, your WordPress site is where your marketing takes place. People who visit your website expect a lot from it. They expect to...
-
How to fix WordPress Permalinks not working
An alternative name for site urls, your WordPress permalinks are an important part of your WordPress site. Without permalinks, your WordPress site can’t reference your urls or locate your website files. This is why WordPress permalinks not working is a problem that needs immediate attention or you risk losing site visitors over a ‘404 page not found’error. Read on to learn how to fix this common WordPress error. What causes WordPress permalinks to stop working? There are different reasons why...
-
Freelance WordPress developer vs a WordPress agency: Pros & Cons
You’ve finally reached WordPress peak just to realize there’s more to it than meets the eye. You now need a WordPress developer's help in order to achieve your site’s goals. The question is, should you hire a freelance WordPress developer or work with a WordPress agency? How do you determine the best option for you? How is one choice different from the other? When should you opt for one choice over the other? By the end of this post you should have the information you need to make an informed...
-
How to create WordPress anchor links
There are different seo tactics at your disposal. But the best ones are those that put your site’s visitors first. WordPress anchor links saves your visitors the time of looking around before they find what they need. But first, you have to know how to create them. Read on to learn how to create WordPress anchor links. What are WordPress anchor links? An anchor link is a type of link you click to go to a specific place on a website page. Anchor links come in handy in long blog posts with a lot of...
-
11 WordPress developer key skills to look for in a developer
When WordPress site owners start experiencing WordPress issues, many wonder if hiring a WordPress developer is worth it. For the most part, yes it is. Provided you hire a developer with necessary WordPress developer key skills. Deducing the skills a WordPress developer should have can sometimes be complicated, especially if you don't understand your WordPress issues, what exactly they need to be fixed, what to look for out for and who to stay away from. By the end of this post, you will be...
-
What is a FTP Client & How to set it up?
Working with WordPress means sometimes you will have to transfer files between your computer and server. Without a control panel, you will need an FTP client to do this successfully. In this guide, we will outline what an FTP client is, why it is important, available options to choose from, and how to set up and use an FTP client. After reading this article you will have the information you need to understand the basics principles, how to set up and use an FTP client. First of all, what is an FTP...
-
How to fix 504 gateway timeout WordPress
Are you trying to access your website and coming across the 504 gateway timeout error? This is a common error for WordPress websites and can be quite alarming when you don’t know why it is happening. The downside of this error is that it does not specify it’s cause, your website becomes inaccessible to your users, and this can directly impact traffic. It is frustrating for you and your potential website visitors… But don’t panic. In this post we are going to find out what causes the 504...
-
How to fix not secure WordPress website (HTTPS secure)
A ‘not secure error’ can be a pretty big deterrent for your potential website visitors as well as unnerving for you the website owner. Knowing why it is happening and how you fix it will help keep your site from displaying this error to future website visitors. This is a common error that occurs when a website does not have an SSL certificate. Here we will walk through the cause and solution to this ‘not secure error’. What causes a WordPress website to be ‘not secure’? As you already know,...
-
Fix 'the link you followed has expired in WordPress'
We’re guessing your site just declared that the 'WordPress link you followed has expired'. While this can be extremely frustrating, worry not, this is a common WordPress error and we can help you fix it. This article will discuss why ‘The link you followed has expired’ error occurs and how to fix this error on your own. What causes ‘The Link You Followed Has Expired Error?’ The WordPress site admin area has a pre-set upload size limit set by your hosting company. The size limit is set to avoid...
-
How to fix WordPress password protected page not working
Many WordPress site owners who offer different hierarchical services through their websites are most probably familiar with the WordPress password protection page feature. Self-explanatory, this feature is used to keep certain pages and posts on a site hidden from the public i.e pages that are reserved for clients only, or staff only. Alternatively, you can use this feature to hide your website login page from the public. Sometimes password protected pages may not work. In this article, we are...
-
How to fix WordPress too many redirects error
Are you locked out of your WordPress website? Are you struggling to access your web pages? Is your WordPress stuck in a redirection loop? These are common WordPress occurrences associated with the “WordPress too many redirects error” In this article we are going to talk about the ‘WordPress too many redirects error’, it’s causes, and how to fix and prevent it. What causes ‘WordPress too many redirects error’? WordPress uses a SEO-friendly form of redirection to assign functioning URLS to your posts...
-
How to fix this site can’t be reached error in WordPress
This site can’t be reached in WordPress is a frustrating error because what are you to do if your site is telling you it can’t be reached. Well, plenty. There are different reasons why your WordPress site is presenting you with this error. A majority of these reasons are not as bad as the ‘consequence’. In this article, we are going to discuss the causes of this error, how to check a specific cause for this error, and how to solve the error. How to check the cause of ‘this site can’t be reached...
-
Fix WordPress stuck in maintenance mode easily
If you often update themes and plugins on your WordPress site then there is a big chance your WordPress is in maintenance mode more than you think. Maintenance mode is part and parcel of a WordPress site. Some WordPress site owners set it up to make major updates to their websites when they don’t have a staging site. This allows them to provide a friendly message to their visitors as well as a timeframe for when the site will be back live. However when WordPress gets stuck in maintenance mode, this...
-
How to fix add media button not working on WordPress
A broken Add media button is one of those confusing and frustrating WordPress problems. Unlike other WordPress issues, the add media button does not present itself as an error nor does it stop your site from working altogether. Instead, it just stops you from adding media to your posts and site. In this article we are going to figure out why the add media button stops working, and how to fix it. What causes the WordPress Add Media button to stop working? WordPress has some dynamic features...
-
How to fix WordPress update fatal error
Did you just update something in WordPress and now your website has what we call a WordPress update fatal error? Don’t panic — this is a common WordPress issue. In this guide we are going to learn about the WordPress update fatal error is, what causes it and how to fix the different fatal errors caused by different WordPress updates. What causes WordPress update fatal error? WordPress update fatal error happens when you update something in WordPress i.e. Plugin, Theme and WordPress core — And that...
-
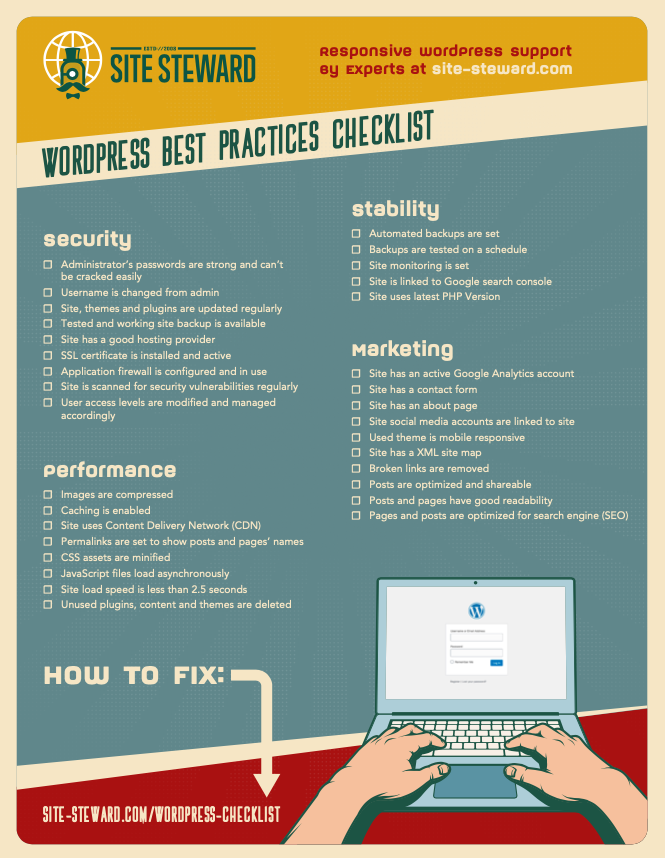
WordPress Best Practices Checklist
A Detailed Guide to Get Your Site Running Optimally Do you ever worry that your WordPress site might not be set up correctly? That you might have installed plugins that could cause problems? Or that you might have vulnerabilities that make your site open to being hacked? We get a lot of questions from customers like these and decided to create a checklist to help site owners like you. This checklist is not just based on our 14+ years in business— we actually went out and interviewed a separate panel of...
-
Find & Hire a WordPress Developer: The Ultimate Guide
When I first started as a freelance developer more than 13 years ago, I charged clients $17/hour. This was an amazing deal for my clients as I was skilled and reliable and just a bit green behind the ears on what it took to make a living (I ate a lot of beans and rice the first couple of years.)